Business efficiency in most cases is determined by the integrity and availability of information, as well as its confidentiality. Today, the most urgent threat in the field of information security (IS) is the leakage of closed data from prohibited user actions. This is due to the fact that traditional tools such as antiviruses and authentication systems no longer provide effective protection against insiders (internal violators).
Intruder: who is this person?
The analysis of protective tools and measures should start by looking at the insider model. Internal offenders are employees or other users who have legal access to confidential information. These include not only people who work on PCs as part of a corporate network in the office. These can be business travelers with office laptops, remote employees, couriers who transport information carriers.
Insiders can be divided into 3 types:
- Offended employee. Such an intruder, when knowingly leaving the organization, copies confidential information in order to use it in another organization and thereby take revenge on the company, which, in his opinion, has acted unfairly with him. Such incidents often occur in the context of massive redundancies.
- Intruded (bribed) employee. In this case, we are talking about industrial espionage. To collect confidential information in a competing company, a company introduces a spy or simply bribes a disloyal employee. This situation is not very common.
- Inattentive employee. Such an employee violates internal security policy, albeit not on purpose. A negligent employee may mistakenly send an e-mail with secret information to the wrong recipient or take home an electronic medium with confidential data and lose the USB flash drive. Practice shows that this type of insider is responsible for most of the leakages.
The course of action, as well as the motives of potential violators, may differ. Thus, the technologies for protecting against internal threats are different.
DLP: what is it?
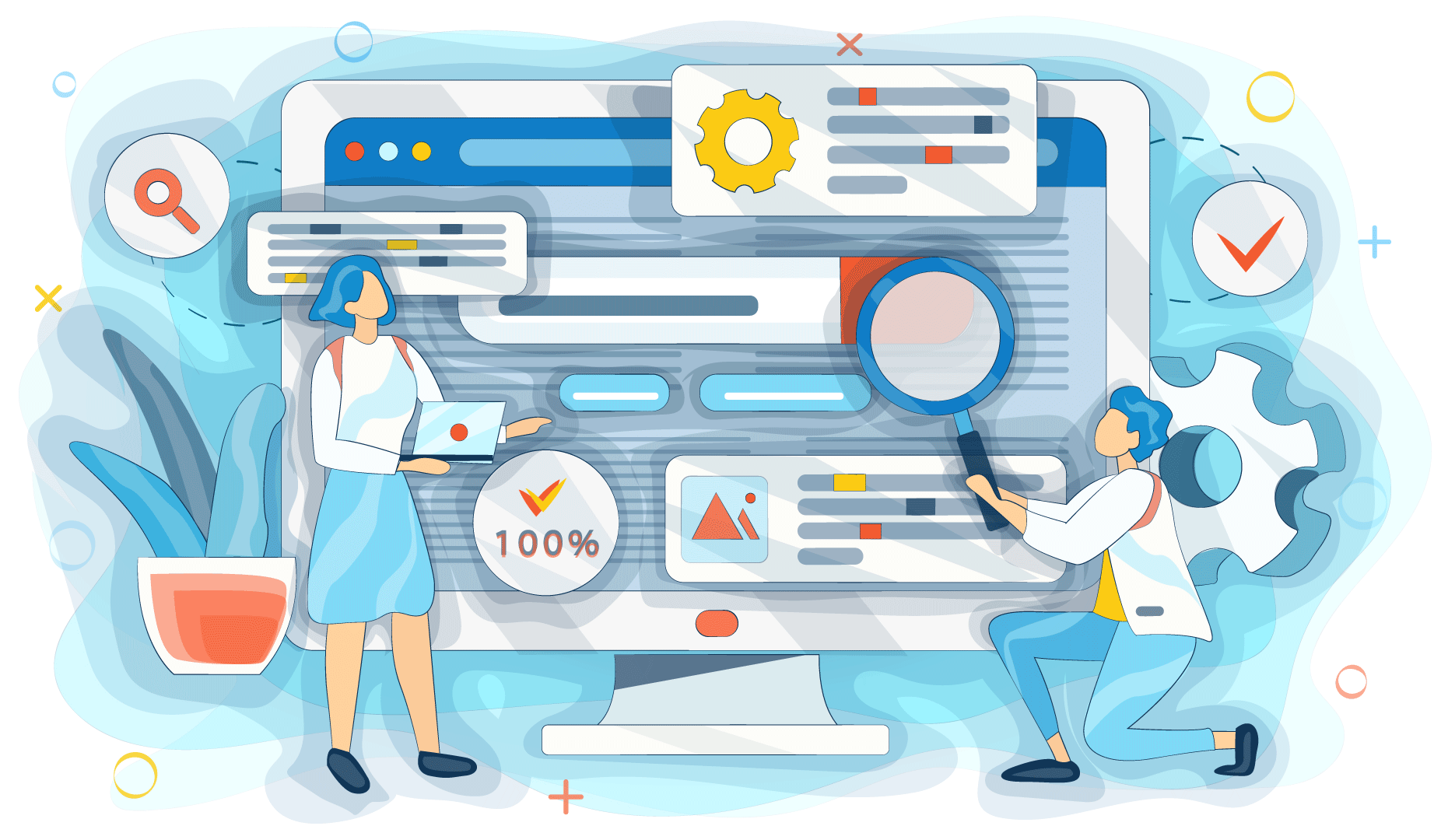
DLP are technologies that prevent the leakage of confidential information. The term "DLP" (data loss prevention) appeared in the lexicon of information security specialists not so long ago. This abbreviation designates systems that both control possible leakage channels and block them in case of an attempt to send secret data through these channels. There are two types of such systems: host and network.
Host DLP
DLPs of this type are installed on every host in the network, they can be used to control Internet traffic. An employee who has brought an MP3 player or portable digital media into the office poses a greater security threat than the most sophisticated hackers. Host DLPs are designed to control external devices as well as printers. These tools allow you to customize access rights for users. For example, one group of employees is prohibited from working with external media, while others are allowed to read-only.
In terms of printer control, host DLPs allow you to save copies of printed documents in a graphical format, so you can analyze them later.
The disadvantages of such a security system include the fact that a user with administrator rights can disable this software in order to commit unauthorized actions.
Network DLP
By the principle of a network gateway, all passing information is filtered. Network DLP allows you to control instant messaging services, outgoing mail, etc. If some sensitive information is found, network DLP blocks such a file. There is a possibility of manual processing of suspicious documents. Such files are placed in quarantine, regularly reviewed by internal security officers, who either allow or deny the transfer.
The main problem of implementing such systems is the way of detecting secret data. To simplify the content analysis, the following detection methods have been developed:
- Tags. They are embedded in documents in order to describe the degree of confidentiality of information, what can be done with this file, and to whom to send it.
- Signatures. One or more sequences of characters are specified, the presence of which in the text of the transmitted document informs the DLP system that the file contains confidential information.
- Morphological analysis. This method is similar to the previous one, the difference is that not an absolute match with the signature is analyzed, but single-root words are taken into account.
- Digital prints. A hash function is calculated for all secret documents, which remains the same or changes insignificantly for any changes in the file.
- Regular expressions. They make it possible to find template information in the text: bank accounts, passport data, etc.
It can be seen from the above list that such methods do not provide a 100% definition of classified information because various kinds of errors are not excluded. Some problems in the operation of network DLP are often created by traffic encryption. However, despite all the difficulties, when properly configured, the use of this system significantly reduces the risk of leakage.
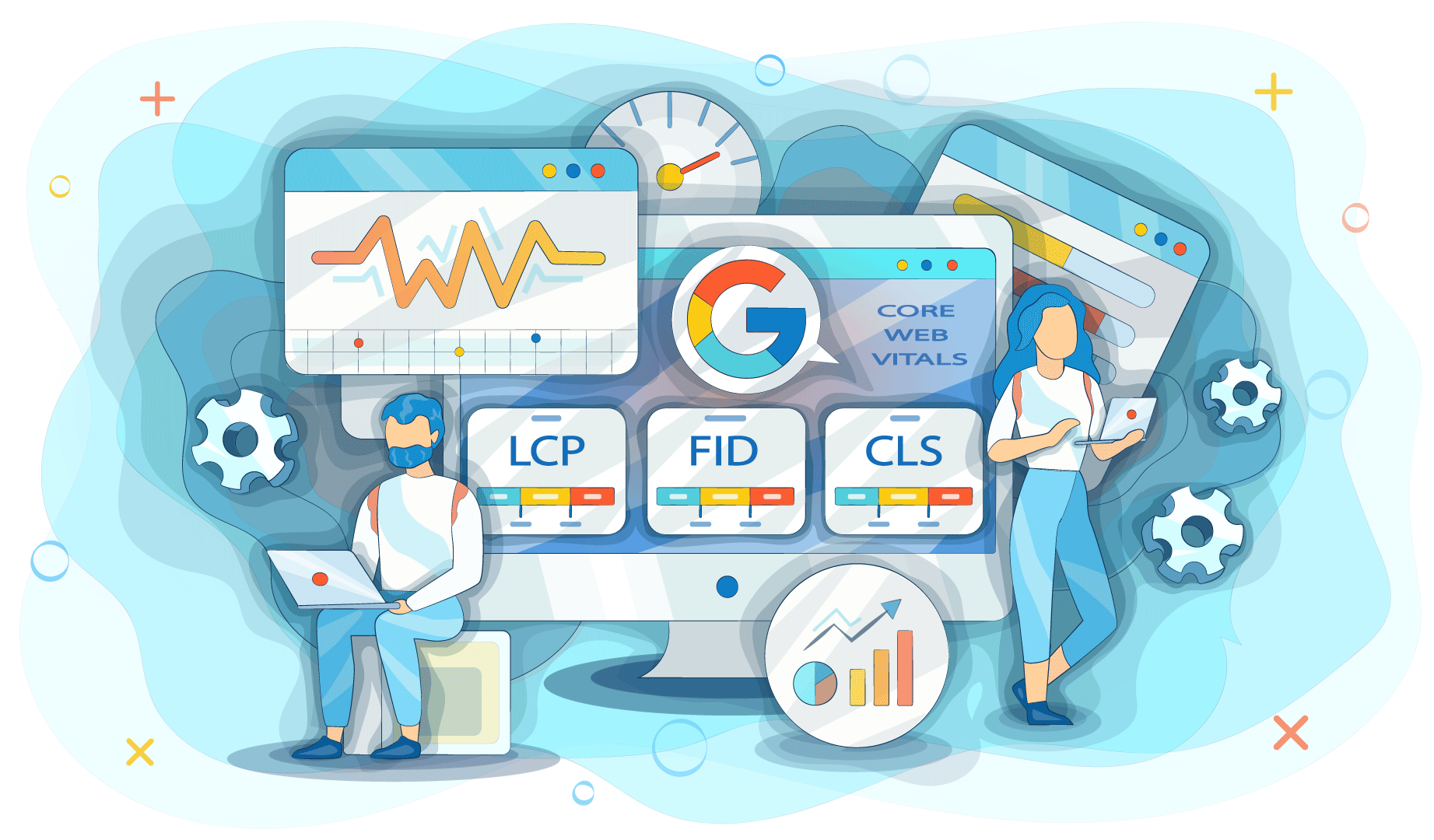
IPC concept
IPC is a logical continuation of DLP technology. It protects not only from data leakage through technical channels, but also from unauthorized user access to the network, applications, and classified information. Thus, IPC avoids the transmission of confidential information in cases where the insider gains direct access to the data. For example, even if a hard drive is seized from a corporate PC, an attacker will not be able to view the files it contains.
The main task of the IPC system is to prevent the transfer of confidential information outside the corporate network. Leakage can be intentional or unintentional. However, more than 75% of attempts to transfer classified information occur due to the carelessness or negligence of company employees. In such cases, IPC is an excellent solution to the problem. When it comes to industrial espionage or competitive intelligence, malicious intruders try to trick IPC analyzers and other systems.
From all of the above, we can draw up the conclusion that the considered DLP and IPC control technologies make it possible to build a fairly reliable internal control system and significantly reduce the risk of leakage. However, they also have their drawbacks, so they cannot always provide 100% protection. At the same time, this area of information security continues to develop, which means that more advanced technologies will be offered. Today, many companies have already made a choice in favor of DLP and IPC, realizing that carelessness in matters of information security can be too expensive.