Data center security is a factor that a client takes into account when looking for a provider. This is because database security is important for every project. Data center information security is a whole range of technical measures that help prevent information leakage and protect files from unauthorized access. The following components require mandatory protection: the data itself, actions for collecting, processing, and transferring information, server users, IT infrastructure.
What is the threat?
Before considering protection methods, you should conduct a risk analysis, clearly define where to expect the threat from.
The following models of threats and offenders are distinguished:
- adverse natural phenomena;
- terrorist attacks;
- dependence on a provider, customers, partners;
- failure in work, any kind of damage;
- internal offenders - data center employees who abuse their powers;
- attempts to unauthorized access to confidential information;
- inconsistency of an informational system with the rules prescribed in the legislation.
The list can be further continued because security is compromised even during power outages.
Risk analysis involves not only identifying possible threats but also assessing the likely negative consequences. Such an approach will help you create an effective action plan, prioritize tasks and budget the funds needed to purchase the right equipment and programs.
Information security should be organized taking into account the requirements of the legislation.
Legal requirements
The methods that are planned to be used to ensure the security of data centers should not contradict legal regulations. Special security conditions should be created for centers cooperating with state information systems. The issue of security is solved even before the introduction of GIS.
Information security: levels
Today, integrated and multi-level information security systems are most often used. They consist of macro-segmentation.
The second level of protection is the detection of internal problems. The data center monitors and checks the dynamics of traffic in order to identify malicious programs that have started the suspicious activity. Large volumes of traffic make it difficult to check everything manually, so the latest algorithms are used for this purpose. These tools find software that is dangerous, even if encryption is used.
The third level is ensuring the information security of the device in the local network. For this purpose, agents are additionally installed that can analyze I/O operations and any file changes. Special algorithms detect the slightest violation of logic.
What does IP protection include
The key to an effective security system is the well-coordinated work of information security specialists and data center personnel. Standards and requirements need to be formalized in writing. Such documentation helps to motivate employees to act according to the recommendations of the security experts.
Protection of engineering components
Power outages and chiller failures negatively impact data center operations. This threat can be prevented. For this, a "smart" control system is being implemented, combining innovative cooling and ventilation systems, as well as power supplies, which can be monitored 24/7 by special controllers.
Protection of the premises
This is especially important if a rental service is being implemented in the building where the data center is located. In this case, it is necessary to prevent unauthorized access.
This type of protection is carried out with the help of fenced parts of the premises, in which round-the-clock video surveillance is also organized. The automatic fire safety system must operate perfectly.
More advanced protective technologies are also present nowadays. These include intelligent control systems when access to the premises is open only to those whose biometrics are included in the database.
In addition, special rooms provide protection against destructive influences from the outside, where service equipment is protected from any potential threat.
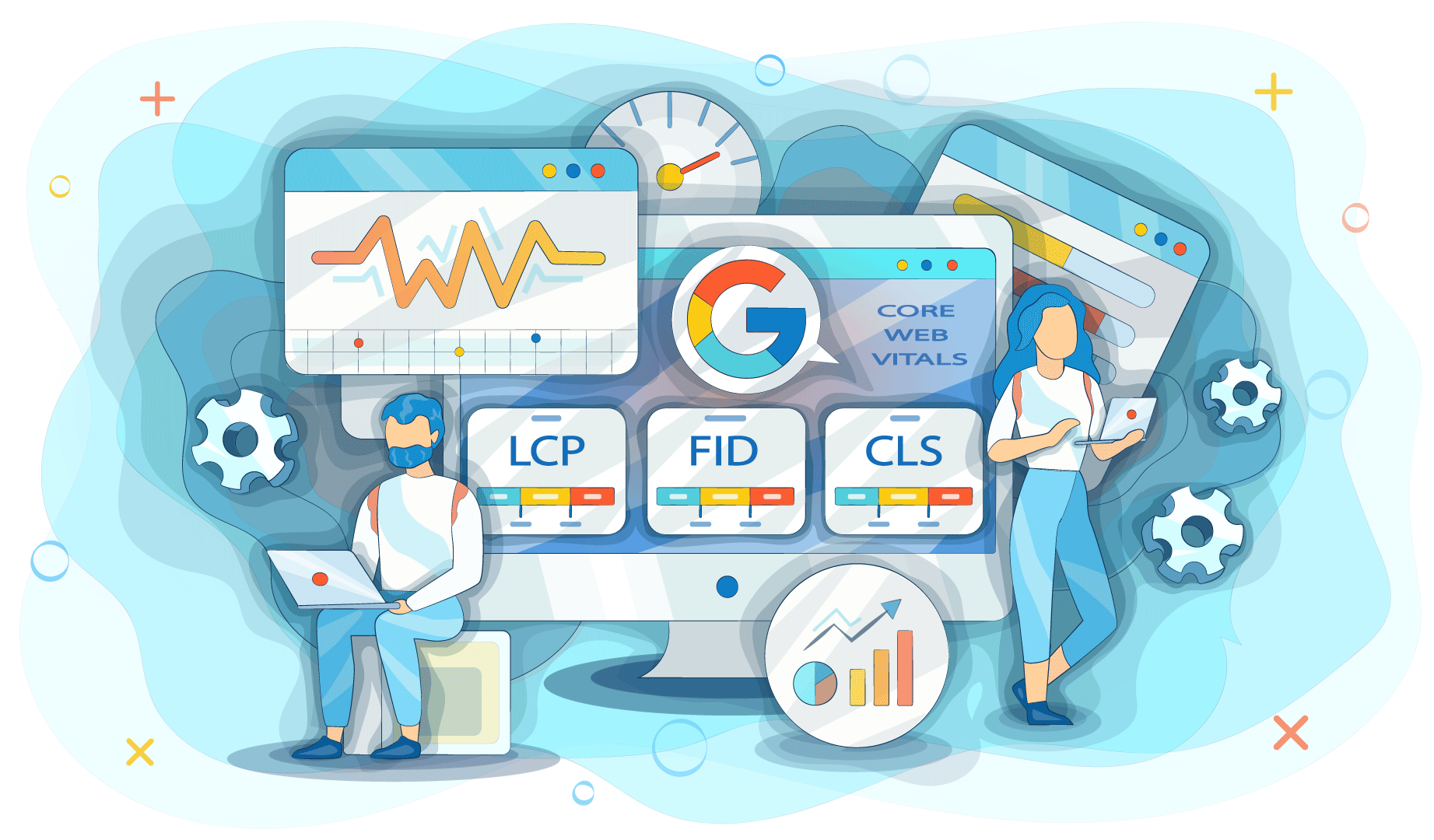
Protection of the virtual environment
The risk always increases when using a VPS. If the infrastructure is interconnected, then a successful attack on one is enough to cause problems for all clients.
To reduce the risk, you should give preference to automated tools. Tools are used that filter incoming network traffic at several levels at once.
Protection of transmission channels
Most data centers lease cloud resources. This means that you need to provide reliable protection for multiple communication channels.
DDoS attacks are dangerous because of the following:
- installation of ransomware viruses;
- blocking the company's infrastructures.
Practice shows that most often companies face the theft or deletion of information that is stored on a cloud service.
You can protect your data with tools that detect and eliminate malicious code.
Let's summarize
Methods for securing data centers continue to evolve. From basic physical methods, most data centers have moved to the use of sophisticated technologies with artificial intelligence.
Speaking about data center security, it's essential to underline the following:
- The use of even the most modern tools does not negate the additional use of special software and hardware.
- Ensuring the security of the data center is impossible without the regular holding of appropriate courses, training for personnel, and the correct organization of information security within the company.
- Data center protection is an ongoing process that requires a constant search for new, more effective solutions.
Thus, ensuring data center security is possible only with competent staff work and the introduction of innovative protection methods.